Two-Factor Authentication: Why You Need a Second Level of Protection
Passwords – they’re everywhere. Include a digit, a special character, a combiNatioN of loWEr and uPpeR case, a symbol.

Tyler Adams
3 min
Two-Factor Authentication
Jul 18, 2021
Apr 22, 2026
How much time do you spend creating countless secure passwords for your accounts, following all the instructions, and using a combination of digits, special characters, and upper- and lowercase letters? Meanwhile, hackers and cyber attacks are getting more sophisticated each day, and your passwords are more vulnerable than ever before.
Secure passwords aren’t enough. No matter how complex and original your password is, there are many ways for scammers to crack it, such as using a computer-powered password generator, intercepting your login information over an unsecured network, finding your phone or other personal device, or simply guessing. You need another layer of security, especially for your business accounts, to protect yourself and your clients.
IT professionals and security analysts have been telling us for a long time that the traditional password is “dead” and have urged people to use additional layers of security for their accounts. That’s where Two-Factor Authentication (2FA) comes in.
Table of Contents
- How Two-Factor Authentication Works
- Why Two-Factor Authentication Is Worth It
- 2FA: An Easy and User Friendly Solution
- Key Takeaways for 2FA
How Two-Factor Authentication Works
2FA is a double layer system of protection that makes your account less vulnerable. It combines multiple forms of verification to ensure that it’s you signing in and not a fraudster trying to gain unauthorized access.
There are three common types of credentials you might use to access an account:
- Something You Know – like a password or a PIN
- Something You Have – such as a phone or an ID badge
- Something You Are – your fingerprint, voiceprint or retinal scan
Some other common types of Two-Factor Authentication include:
- A pre-generated list of one time codes: Secure institutions, such as banks, will sometimes issue a list of pre-generated codes to clients. These codes are used to verify the person’s identity before performing actions such as financial transactions or account recovery.
- A one-time verification code from an authenticator app: These apps can be downloaded directly onto individuals’ mobile devices. Similar to receiving a text or email, the user is sent a one-time code from the app to be used as the second authentication when signing into an account.
- Location: Many devices check an individual’s location by default when signing into an account. The account holder is only alerted if something is amiss and the sign-in attempt is coming from somewhere unexpected. If this happens, another form of verification will be triggered.
- Security key: This is a physical device that uses cryptography to authorize a user’s login. It is connected to another device, such as a desktop, laptop, or phone and is integrated with the primary device using software. Security keys are expensive to implement, but offer a high level of security.
Why 2FA Authentication Is Worth It
Adding another step to your login process might seem difficult or like a waste of time. In reality, the pros far outweigh the cons.
Using only one layer of security is too risky, especially for businesses handling large transactions, due to the prevalence of hacking, key logging, social engineering, man in the middle attacks, and other techniques used by scammers. If one of your accounts is compromised, so are all other accounts with the same login credentials. Even if hackers only know your username, they can use software to guess your passwords. Considering what’s at stake for you and your clients if your data is compromised, not implementing 2FA is dangerous.
If a data breach does occur and hackers get ahold of your credentials, the consequences could be severe. You could experience identity theft, monetary theft, system sabotage, and/or reputational damage.
2FA makes it much more difficult for hackers to break into your accounts and steal your data. With 2FA, your accounts are secured with information only you or your devices can access, making hackers’ authentication attempts much less successful. If protecting your data is a priority, 2FA should be added to your accounts.
2FA: An Easy and User Friendly Solution
Most 2FA systems, once implemented, are easy to use and make your accounts significantly more secure. You’ll still have to remember your username and password, but the second security layer doesn’t involve remembering anything. For example, 2FA could come in the form of a push notification or text message sent to your mobile phone. Since most people carry their phones with them at all times, completing that second layer of authentication is easily achievable. Additionally, most website service accounts support 2FA, and all it requires is activating it in the settings. Sites like TwoFactorAuth can help you determine what services offer 2FA.
Your IT professional should be able to set up 2FA for any critical business accounts, or you can employ a vendor to provide multi-factor authentication (MFA) for you, such as Symantec VIP or Vasco Identikey. More sophisticated 2FA systems, such as those that use biometrics, will require a more significant financial investment and may take more time to implement.
Key Takeaways for 2FA
Instituting 2FA for all your business accounts is an effective way to keep you and your clients safer from hackers. Given the large amounts of money and personal information that’s exchanged during real estate transactions, it’s essential that your accounts be protected with 2FA.
Remember that 2FA:
- Provides a double layer of protection;
- Makes it so that only you can access your accounts;
- Helps you avoid data breaches; and
- Is simple to implement and use.
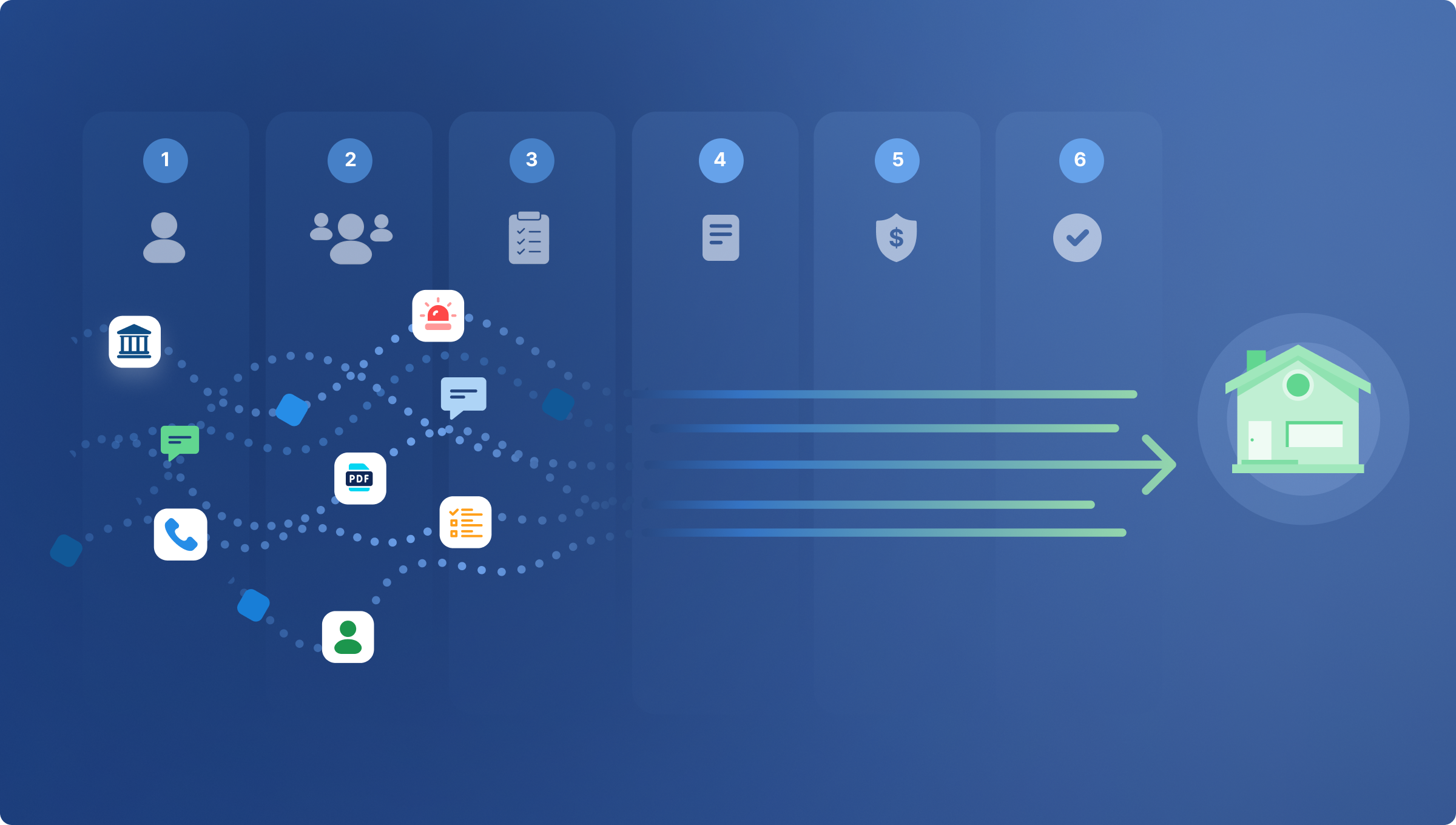
CertifID is here to help you and your business and can advise on best practices, like 2FA, to make sure you’re protected from cyber criminals. The below infographic provides a concise overview of steps you should take to prevent yourself from fraud.
Interested in learning more? Contact CertifID today to find out about our products and services.
.png)
FAQ
Co-founder & CEO
Tyler brings a decade of leadership experience developing and launching technology businesses. Before co-founding CertifID, Tyler led new product development at BCG Digital Ventures for Mercedes-Benz, First American Financial, Boston Scientific, and Aflac.
How much time do you spend creating countless secure passwords for your accounts, following all the instructions, and using a combination of digits, special characters, and upper- and lowercase letters? Meanwhile, hackers and cyber attacks are getting more sophisticated each day, and your passwords are more vulnerable than ever before.
Secure passwords aren’t enough. No matter how complex and original your password is, there are many ways for scammers to crack it, such as using a computer-powered password generator, intercepting your login information over an unsecured network, finding your phone or other personal device, or simply guessing. You need another layer of security, especially for your business accounts, to protect yourself and your clients.
IT professionals and security analysts have been telling us for a long time that the traditional password is “dead” and have urged people to use additional layers of security for their accounts. That’s where Two-Factor Authentication (2FA) comes in.
Table of Contents
- How Two-Factor Authentication Works
- Why Two-Factor Authentication Is Worth It
- 2FA: An Easy and User Friendly Solution
- Key Takeaways for 2FA
How Two-Factor Authentication Works
2FA is a double layer system of protection that makes your account less vulnerable. It combines multiple forms of verification to ensure that it’s you signing in and not a fraudster trying to gain unauthorized access.
There are three common types of credentials you might use to access an account:
- Something You Know – like a password or a PIN
- Something You Have – such as a phone or an ID badge
- Something You Are – your fingerprint, voiceprint or retinal scan
Some other common types of Two-Factor Authentication include:
- A pre-generated list of one time codes: Secure institutions, such as banks, will sometimes issue a list of pre-generated codes to clients. These codes are used to verify the person’s identity before performing actions such as financial transactions or account recovery.
- A one-time verification code from an authenticator app: These apps can be downloaded directly onto individuals’ mobile devices. Similar to receiving a text or email, the user is sent a one-time code from the app to be used as the second authentication when signing into an account.
- Location: Many devices check an individual’s location by default when signing into an account. The account holder is only alerted if something is amiss and the sign-in attempt is coming from somewhere unexpected. If this happens, another form of verification will be triggered.
- Security key: This is a physical device that uses cryptography to authorize a user’s login. It is connected to another device, such as a desktop, laptop, or phone and is integrated with the primary device using software. Security keys are expensive to implement, but offer a high level of security.
Why 2FA Authentication Is Worth It
Adding another step to your login process might seem difficult or like a waste of time. In reality, the pros far outweigh the cons.
Using only one layer of security is too risky, especially for businesses handling large transactions, due to the prevalence of hacking, key logging, social engineering, man in the middle attacks, and other techniques used by scammers. If one of your accounts is compromised, so are all other accounts with the same login credentials. Even if hackers only know your username, they can use software to guess your passwords. Considering what’s at stake for you and your clients if your data is compromised, not implementing 2FA is dangerous.
If a data breach does occur and hackers get ahold of your credentials, the consequences could be severe. You could experience identity theft, monetary theft, system sabotage, and/or reputational damage.
2FA makes it much more difficult for hackers to break into your accounts and steal your data. With 2FA, your accounts are secured with information only you or your devices can access, making hackers’ authentication attempts much less successful. If protecting your data is a priority, 2FA should be added to your accounts.
2FA: An Easy and User Friendly Solution
Most 2FA systems, once implemented, are easy to use and make your accounts significantly more secure. You’ll still have to remember your username and password, but the second security layer doesn’t involve remembering anything. For example, 2FA could come in the form of a push notification or text message sent to your mobile phone. Since most people carry their phones with them at all times, completing that second layer of authentication is easily achievable. Additionally, most website service accounts support 2FA, and all it requires is activating it in the settings. Sites like TwoFactorAuth can help you determine what services offer 2FA.
Your IT professional should be able to set up 2FA for any critical business accounts, or you can employ a vendor to provide multi-factor authentication (MFA) for you, such as Symantec VIP or Vasco Identikey. More sophisticated 2FA systems, such as those that use biometrics, will require a more significant financial investment and may take more time to implement.
Key Takeaways for 2FA
Instituting 2FA for all your business accounts is an effective way to keep you and your clients safer from hackers. Given the large amounts of money and personal information that’s exchanged during real estate transactions, it’s essential that your accounts be protected with 2FA.
Remember that 2FA:
- Provides a double layer of protection;
- Makes it so that only you can access your accounts;
- Helps you avoid data breaches; and
- Is simple to implement and use.
CertifID is here to help you and your business and can advise on best practices, like 2FA, to make sure you’re protected from cyber criminals. The below infographic provides a concise overview of steps you should take to prevent yourself from fraud.
Interested in learning more? Contact CertifID today to find out about our products and services.
.png)
Co-founder & CEO
Tyler brings a decade of leadership experience developing and launching technology businesses. Before co-founding CertifID, Tyler led new product development at BCG Digital Ventures for Mercedes-Benz, First American Financial, Boston Scientific, and Aflac.
Sign up for The Wire to join the conversation.